Infinity – Hacking like a Pro
6 Minute Read
Mar 19 2013
Advertisement
Levitas here to take a look at the Hacking mechanic in Infinity. It’s not just a keyboard in a gunfight…
Hacking
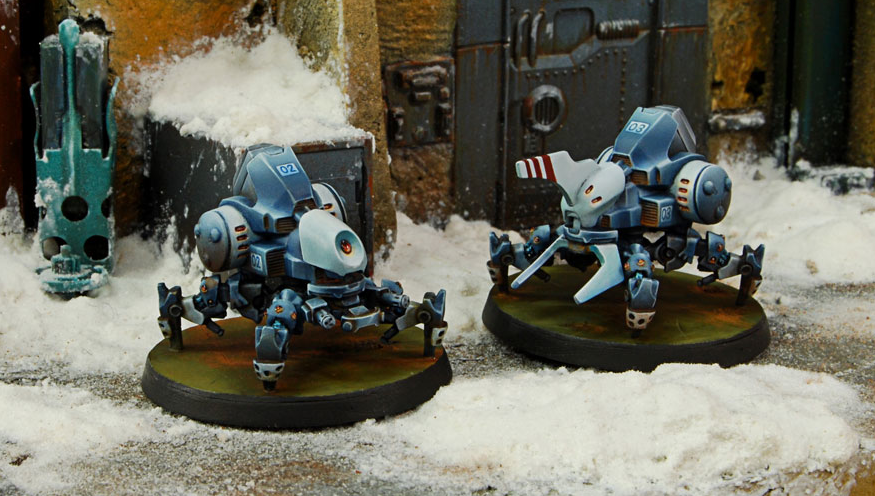
Info war is a big part of the Infinity future combat universe. Often you don’t need to fill a heavy infantry with holes, you can just turn it off instead. Teams can send a remote to do a mans job, or put a soldier inside a giant death dealing suit of doom. AKA the TAG (Tactical Armored Gear).
What this means is there is a lot of tech on the board. Tech that can be manipulated by a quantronic artist. These are specialists in infowar, cyber assault, electronic combat and defence. The Hackers.
Who can hack?
Hacking uses the Will Power stat, which is then modified by the targets BTS instead of armor value. Serious hackers also bring equipment that can reduce that BTS, often making a mockery of the most well armored unit. Imprisoning them in their armor, with only the faint smell of pee for company.
Most factions have several options for hackers. Specific units with access to hacking devices, but it doesn’t always mean they are good at it. Basic line troops often have a hacker option, and while useful they don’t always cut it like a pro. But they can be handy for quick and dirty defensive hacking.
Worth noting that Ariadna are not known for their hackers, as their background dictates a lower level of tech compared to the other factions. But they do have wolf men in kilts, so you know…it balances…
What Can Hackers Do?
Beside look cool typing really fast on their glowing displays? Well, hackers have a few modes to play with.
• Attack Mode:
A short Order used to hack T.A.G.s, Remotes (REM), Heavy Infantry (HI), Doors, and Security/Data targets. It is also used to perform cyberattacks against other Hackers.
These are all targets that can cause problems in direct conflict. Especially multi wound TAGs and Heavy Infantry. There are situations where hackers can really shine; especially as they don’t need line of sight to hack attack them. Thus negating a potentially lethal ARO.
The last one, cyber attack against another hacker, is also very cool. And often ends with a head exploding after a titanic cyber duel. This can be a handy way to get to a enemy hacker who is dug in, and well out of harms way.
Offensive hacking is limited by range, but I’ll get to that.
• Defensive Mode
This is used to defend allied miniatures from Hacking Attacks, Guided Missiles and the use of Airborne Deployment: Combat Jump. A Hacker in Defensive Mode also operates, hacks, or defends without distance limit.
This is where cheaper hackers can come into play, often used to protect TAGs and HI from getting their pretty suits turned off like a light bulb. They can do this as an ARO, jumping in to save an ally from any where on the board.
Swatting guided missiles out of the air is hard, but a better solution than taking the violent and destructive explosion to the face. Again, they can do this from anywhere as an ARO.
Hacking Airborne Deployment: Combat Jump is like shaking the tree, and seeing if the cat falls out. Or even a heavy machine gun toting drop troop. Much like taking on guided missiles, it isn’t easy, but it is worth it to see your opponents surprise tactic taken from them.
• Other functions of Hacking Devices
Hackers can also be taken to open up the use of Remotes, as well as perform in game objectives. The new Paradiso book in particular often calls for hackers to open doors, steal information, and shut down security guns etc.
Hacking Like a Pro
So those are the basics, but there is a lot of depth to the hacking mechanic. Let this Nomad player tell you more…
Repeaters and Markers.
Serious hacking requires the use of repeaters. These allow a hacker to extend their range by using the zone of control of the repeater, no matter where the hacker is on the board. As I mentioned before, no line of sight is needed. So a repeater could be hidden behind a wall, and a hacker can attack anything that comes with 8″ of it. Even if the cyber assassin is nestled in cover many inches away.
Other hackers carry repeaters, as do TAGs and most Remotes. So it’s not hard to create multiple hacking threats and weave a cyber web ready to ensnare a fool hardy target.
Markers are weapons that can fire deployable repeaters, often with limited ammo. But again this lets you put a repeater where you want it, and significantly extends the threat range. The downside is they can be shot off the board. Boo!
Hacking Device Plus
It has plus in the title, so you know it’s good. The HD+ lets hackers also mark targets through their hacking equipment as if they were Forward Observers. Which also means that they carry a Flash Pulse for blinding opponents too. So when you add in repeaters, you can see how easy it can be to set up sneaky attacks with guided missiles, and other spec fire weaponry.
This makes high profile hackers even more dangerous, and reason enough to bring a cheap defensive hacker in most lists. The pricier hackers do more than hack, which they are already good at.
Evo Repeaters
The gold standard includes Evo Repeaters. The presence of an EVO Repeater increases the lethal capacity of hackers, providing a greater power over enemy equipment and systems. As a humble remote they do little in the way of fighting, but they significantly buff hackers. They are usually pretty cheap points wise, and even give benefits in Paradiso missions.
You can use them in a number of ways, but only one at a time:
• Icebreaker lets the hacker halve the BTS value of the target, rounding up. This can make a TAG really sweat. You can also use it to halve the BTS of airborne craft…
• Capture means the hacker only makes one roll to take over an enemy TAG. Needless to say this can be horrendous for your opponent as his point heavy machine mows down his own troops.
• Support Hacking. Up to three Hackers can spend an Order each to give support to a companion. Each hacker supporting provides a +3 Modifier to the hacking roll of the supported figure.
• Trajectory Assistant lets you spend an order to add +3 to the physical test of troops dropping in via combat jump. A nice laser guided delivery of that nasty shock troop right where you want them, which is extremely handy.
Hacking from Camo
Like regular attacks, striking from camo usually lets you get the jump on your opponent. And what if they can infiltrate too? Well that gives you repeaters to hack through very early in the game. Combine with an EVO repeater and you can shut down that TAG or Heavy Infantry before they can say spam mail.
Conclusion
As you can see there are a ton of benefits to taking a hacker. You just have to decide how serious your list will be, as pro hacking requires a few extra toys. But then you might face a list with nothing to hack, and I have definitely been there. When it does come off though, it is extremely effective.
The defensive value of them is also worth considering. If you do run a pricey TAG then you don’t want to see it shut down by a plucky hacker.
Hope I’ve given you food for thought. I’ve only scratched the surface of what you can do with hacking mechanic, so play around and have fun.
For more info on Infinity, check out the official site
http://www.infinitythegame.com
You can also see what I am up to with my own Infinity minis at
http://levitas-master-artificer.blogspot.com/
For more info on Infinity, check out the official site
http://www.infinitythegame.com
You can also see what I am up to with my own Infinity minis at
http://levitas-master-artificer.blogspot.com/
What’s your favorite hacking tactic?
How do you combat them?
Are you a Nigerian prince who has recently come into some funds?
Author: John Archer
Advertisement